No products in the cart.
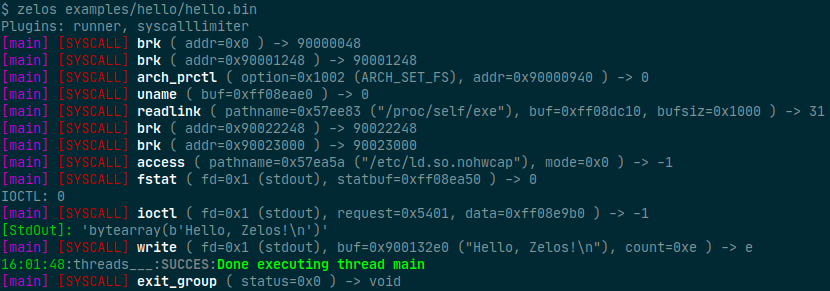
Zelos (Zeropoint Emulated Lightweight Operating System) is a python-based binary emulation platform. One use of zelos is to quickly assess the dynamic behavior of binaries via command-line or python scripts. All syscalls are emulated to isolate the target binary. Linux x86_64 (32- and 64-bit), ARM and MIPS binaries are supported. Unicorn provides CPU emulation. Full documentation is available here. Installation Use the package manager pip to install zelos. pip install zelos Basic Usage Command-line To emulate a binary with default options: $ zelos my_binary To view the instructions that are being executed, add the -v flag: $ zelos -v my_binary You can print only the first time each instruction is executed, rather than every execution, using --fasttrace: $ zelos -v --fasttrace my_binary By default, syscalls are emitted on stdout. To write syscalls to a file instead, use the --strace flag: $ zelos --strace path/to/file my_binary Specify any command line arguments after the binary name: $ zelos my_binary arg1 arg2 Programmatic import zelos z = zelos.Zelos("my_binary") z.start(timeout=3)....
Subscribe
0 Comments