No products in the cart.
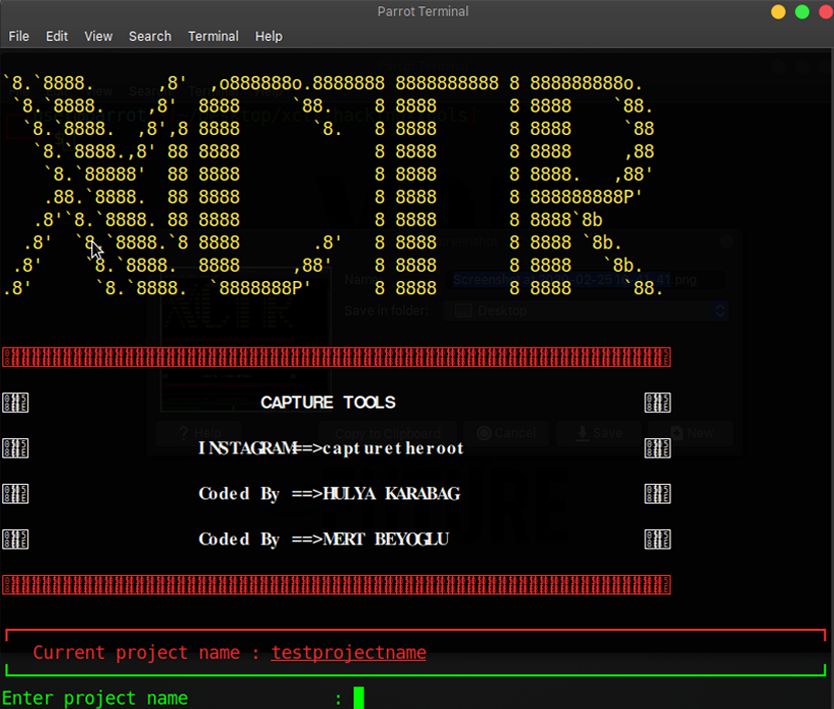
???? Read Me ???? Initially, you need to create a project where you will save everything. All of the collected information is saved as "project-name" in the results directory. ⚙️ You can update user agent and proxy information in the settings section and also update URL, proxy, project name, wordlist, thread numbers. Features This tool includes: Dork Finder Admin Panel Finder Cms Finder Ip History Reverse Ip Page Viewer Proxy Finder ???? Installation ???? Installation with requirements.txt git clone https://github.com/capture0x/XCTR-Hacking-Tools/ cd xctr-hacking-tools pip3 install -r requirements.txt Usage python3 xctr.py All results save in results/project-name. Dork Finder The dork finder has 2 sections. Bing and Yandex. e.g: *.php?id= Admin Panel Finder In this section, firstly need to choose a wordlist for scanning. Press 2 to change the wordlist and log in. Url should be https://targetsite.com/ (HTTP or s and / symbol at the end of the URL.) If scanning is slow....
Subscribe
0 Comments