No products in the cart.
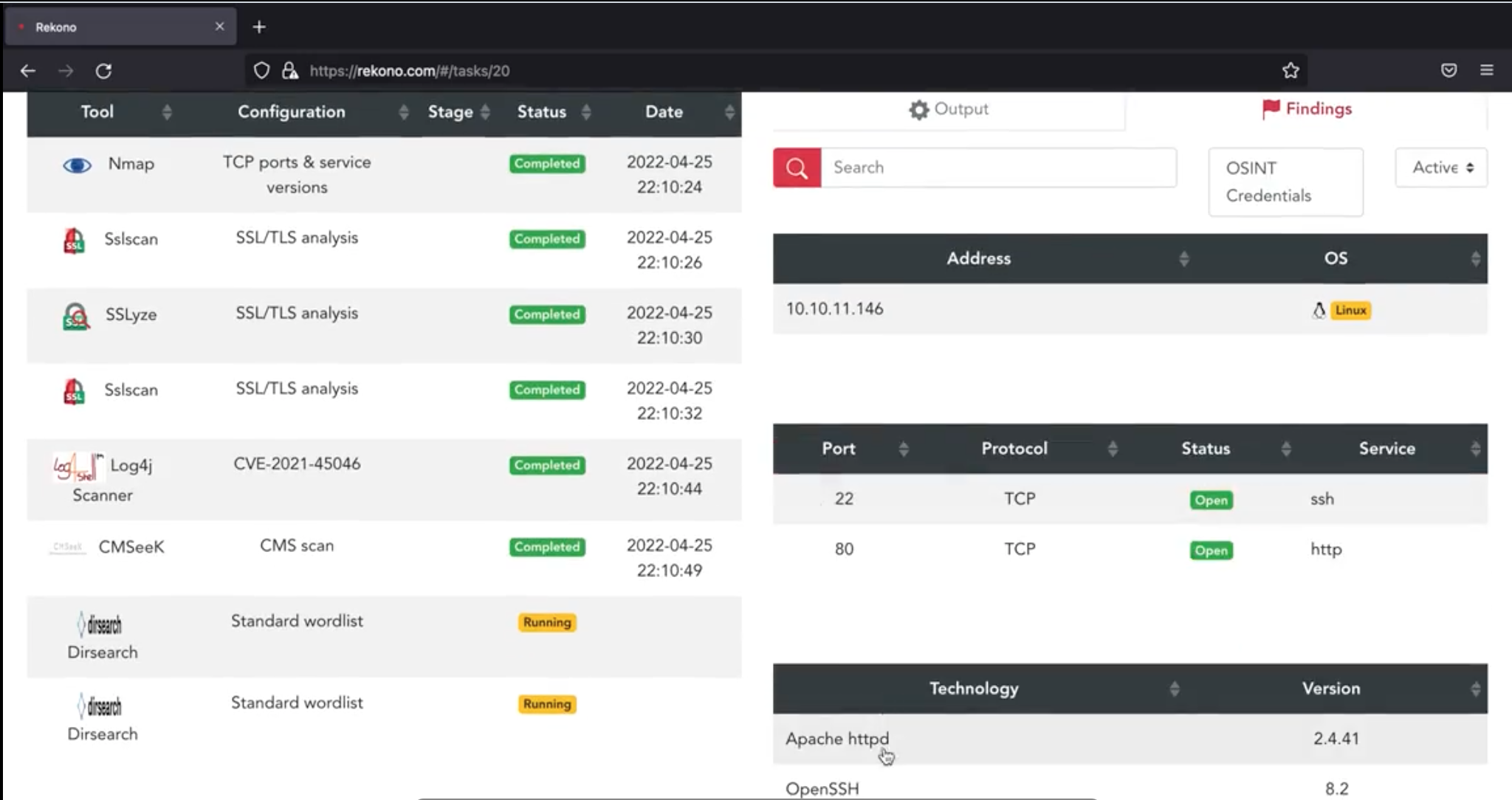
Rekono combines other hacking tools and their results to execute complete pentesting processes against a target in an automated way. The findings obtained during the executions will be sent to the user via email or Telegram notifications and also can be imported into Defect-Dojo if advanced vulnerability management is needed. Moreover, Rekono includes a Telegram bot that can be used to perform executions easily from anywhere and using any device. https://github.com/pablosnt/rekono Features Combine hacking tools to create pentesting processes Execute pentesting processes Execute pentesting tools Review findings and receive them via email or Telegram notifications Use Defect-Dojo integration to import the findings detected by Rekono Execute tools and processes from Telegram Bot Wordlists management Why Rekono? Do you ever think about the steps that you follow when starting a pentesting? Probably you start performing some OSINT tasks to gather public information about the target. Then, maybe you run hosts discovery....
A very big thanks to kelvinethicalhacker at gmail com for the great the work you done for me, i got the email address on the net web when i needed to hack my husband cell phone he helped me within few hours with whatsApp hacking and GPS location tracking direct from my person phone i know how my husband walks, thanks for the helped you do for me for every grateful for your helped, you can contact him through gmail via kelvinethicalhacker at gmail.com or Telegram, calls, text, number +1(341)465-4599, if you are in needed of hacking services, contact him..
It was a few days ago when I discovered my spouse was hiding a lot of things from me and I needed to gain access to the device, I went on Google and saw (kelvinethicalhacker at gmail.com). and it was a great experience, I got access and saw everything my partner was hiding. This life is just amazing.
A great hacker is really worthy of good recommendation , Henry
really help to get all the evidence i needed against my husband and
and i was able to confront him with this details from this great hacker
to get an amazing service done with the help ,he is good with what he does and the charges are affordable, I think all I owe him is publicity for a great work done via, Henryclarkethicalhacker at gmail com, and you can text, call him on whatsapp him on +12014305865, or +17736092741,