No products in the cart.
Stowaway is Multi-hop proxy tool for security researchers and pentesters. Users can easily proxy their network traffic to intranet nodes (multi-layer).
Note: The files under demo folder are Stowaway's beta version,it's still functional, you can check the detail by README.md file under the demo folder.
This tool is limited to security research and teaching, and the user bears all legal and related responsibilities caused by the use of this tool! The author does not assume any legal and related responsibilities!
Features
- obvious node topology
- multi-hop socks5 traffic proxy
- multi-hop ssh traffic proxy
- remote interactive shell
- network traffic encryption with AES-256(CBC mode)
- support macos and linux
Usage
Stowaway can be executed as two kinds of mode: admin & agent. If you don't want to compile the project by yourself, you can check the release tag to get ONE!
Simple example:
Admin mode:./stowaway admin -l 9999 -s 123
Meaning:
admin It means Stowaway is started as admin mode
-l It means Stowaway is listening on port 9999 and waiting for incoming connection
-s It means Stowaway has used 123 as the encrypt key during the communication
Be aware! -s option's value must be as same as the agents'
For now, there are only three options above are supported!
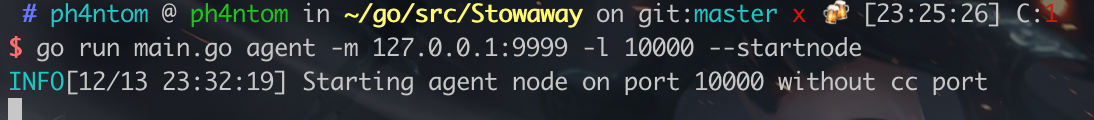
agent mode: ./stowaway agent -m 127.0.0.1:9999 -l 10000 --startnode -s 123 -r
Meaning:
agent It means Stowaway is started as agent mode
-m It means Stowaway's monitor node's address (In this case,it's the node we started above)
-l It means Stowaway is listening on port 10000 and waiting for incoming connection
-s It means Stowaway has used 123 as the encrypt key during the communication
--startnode It means Stowaway is started as FIRST agent node(if the node is the first one , you MUST add this option!!! And there are two submode of agent mode,if you want to start the second, third one....., just remove this option)
-r It means you want to start the node in reverse mode(For instance: you can add node 2 into the net via node 1 actively connect to node 2, instead of node 1 just waiting for the connection from node 2 )
Be aware! -s option's value must be as same as the agents'
For now, there are only five options above are supported!
Example
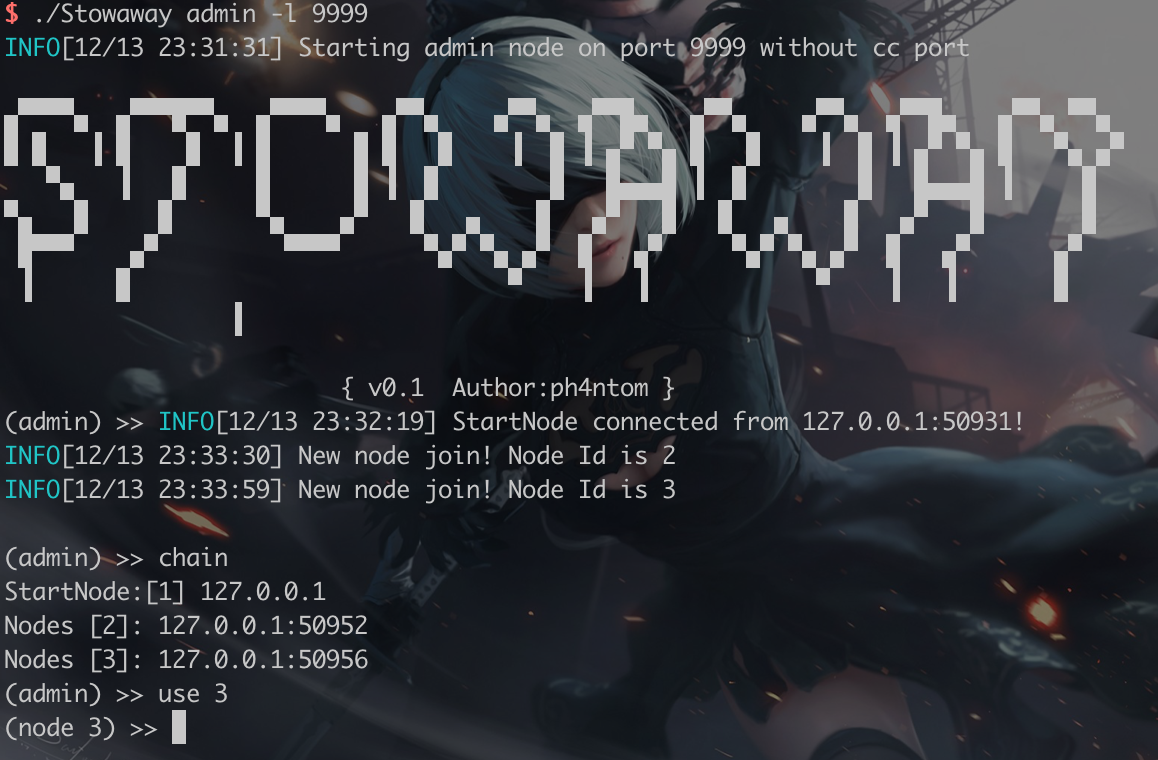
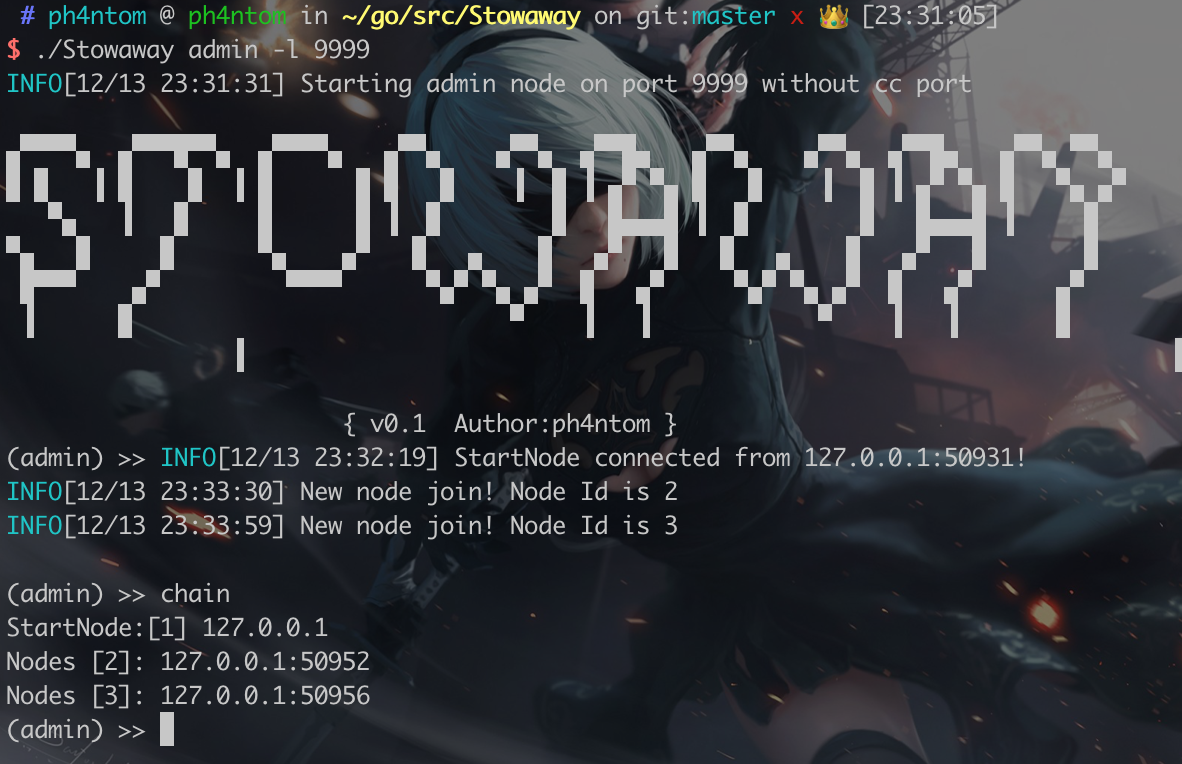
Admin:
Startnode:
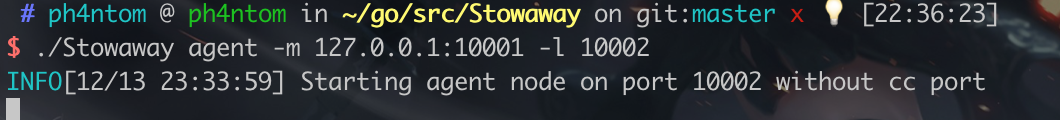
First simple Node(setting as reverse mode:
Now, use admin node and type in "use 1" -> "connect 127.0.0.1:10001", then you can add node 1 into the net. Second simple Node:
When all agent nodes connected, check the topology in admin:
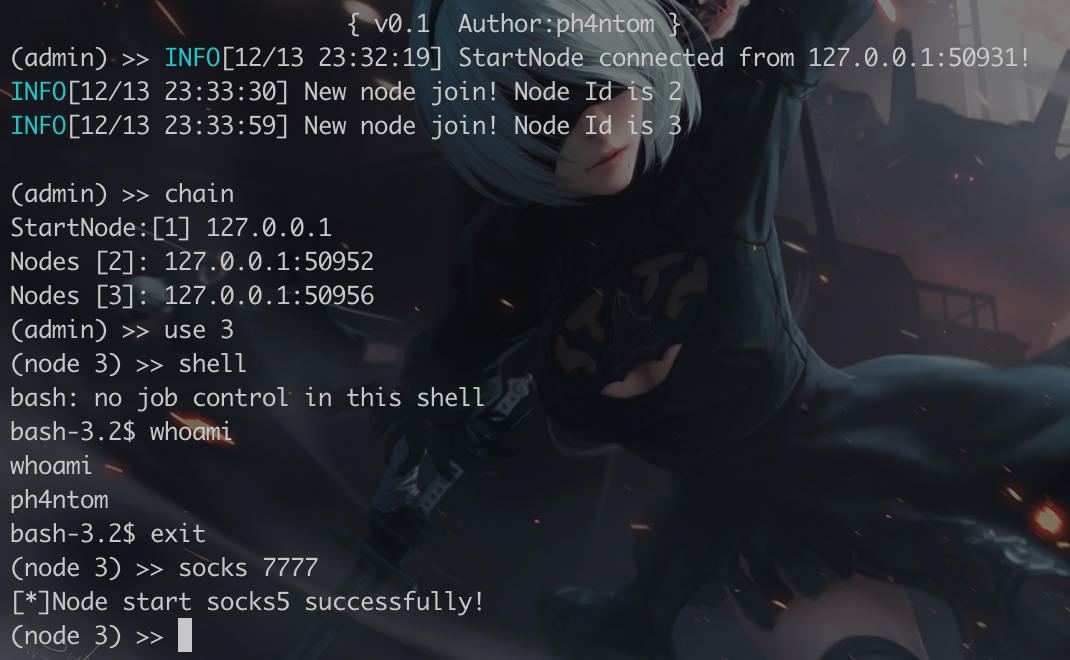
Now we manipulate the second simple node through admin:
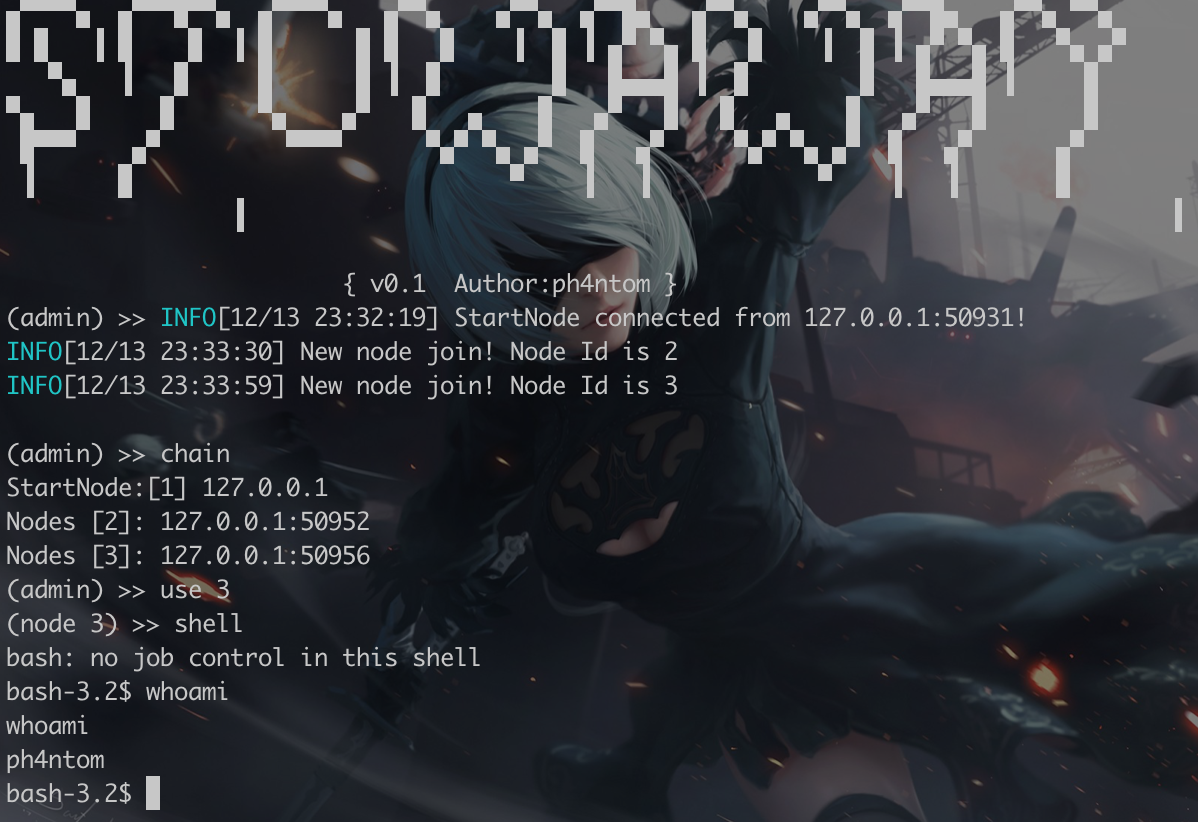
Open the remote interactive shell:
Now you can use interactive shell (the second simple node's) through admin.
Start socks5 proxy service:
Now you can use the admin's port 7777 as the socks5 proxy service.
And it can proxy your traffic to the second simple node and the second simple node will do its work as socks server When you want to shut down this socks5 service, just type in "stopsocks" under this mode to turn off it).
Open ssh:
And it can proxy your ssh traffic to the second simple node and the second simple node will do its work as ssh client.
Note: In this function, you can type in pwd to check where you currently are:
For more detail, just type help to get further informations
TODO
- Network traffic encryption
- Method to turn off socks5 proxy
- Reconnection
- Clean codes, optimize logic
- Add cc function
- Add reverse connect mode
Attention
- This porject is coding just for fun , the logic structure and code structure are not strict enough, please don't be so serious about it
- When the admin offline, all agent nodes will offline too(maybe it will be changed in future)
- When one of the agents offline, the agent nodes after it will offline
- Once the admin started, you need to connect at least one agent node to it before you do any operations
- If you want to compile this project for supporting more platform, you can use
go build -ldflags="-w -s"to do that - Temporarily does not support Windows
Thanks
Main website: https://github.com/ph4ntonn/Stowaway/blob/master/README_EN.md
Subscribe
0 Comments