No products in the cart.
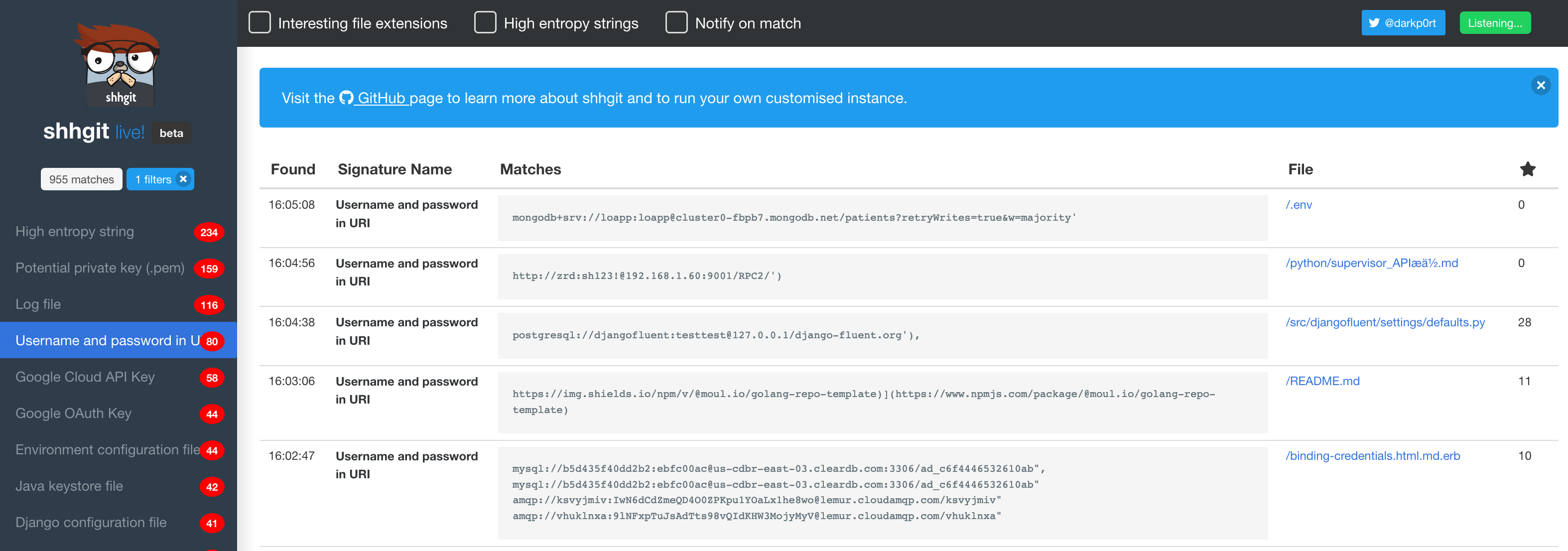
Love shhgit? Help me reach my goal by sponsoring me via GitHub: https://github.com/sponsors/eth0izzle/ NEW: LIVE VERSION. Find secrets find from your browser! Finding secrets in GitHub is nothing new. There are many great tools available to help with this depending on which side of the fence you sit. On the adversarial side, popular tools such as gitrob and truggleHog focus on digging in to commit history to find secret tokens from specific repositories, users or organisations. On the defensive side, GitHub themselves are actively scanning for secrets through their token scanning project. Their objective is to identify secret tokens within committed code in real-time and notify the service provider to action. So in theory, if any AWS secret keys are committed to GitHub, Amazon will be notified and automatically revoke them. I developed shhgit to raise awareness and bring to life the prevalence of this issue. I hope GitHub will....
Subscribe
0 Comments