No products in the cart.
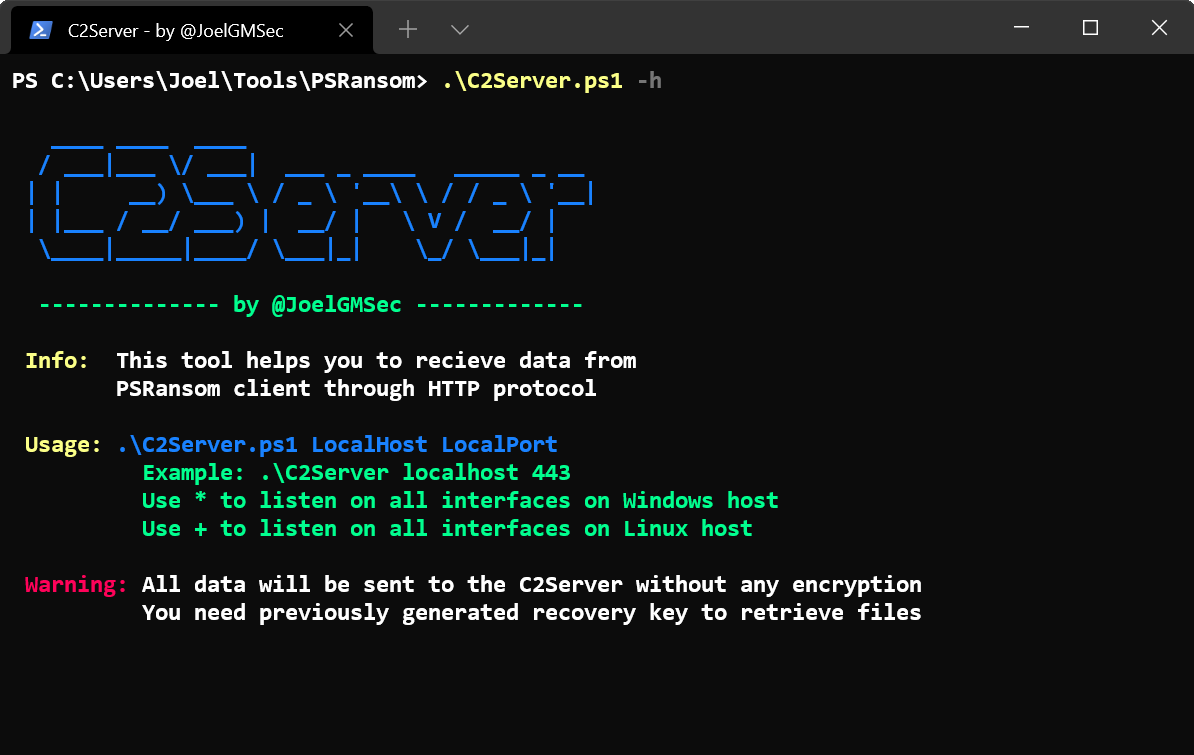
PSRansom is a PowerShell Ransomware Simulator with C2 Server capabilities. This tool helps you simulate the encryption process of generic ransomware in any system on any system with PowerShell installed on it. Thanks to the integrated C2 server, you can exfiltrate files and receive client information via HTTP. All communication between the two elements is encrypted or encoded so as to be undetected by traffic inspection mechanisms, although at no time is HTTPS used at any time. Blog: https://darkbyte.net Github: https://github.com/JoelGMSec/PSRansom Requirements PowerShell 4.0 or greater Download It is recommended to clone the complete repository or download the zip file. You can do this by running the following command: git clone https://github.com/JoelGMSec/PSRansom Usage .\PSRansom -h ____ ____ ____ | _ \/ ___|| _ \ __ _ _ __ ___ ___ _ __ ___ | |_) \___ \| |_) / _' | '_ \/ __|/ _ \| '_ ' _ \....
A very big thanks to kelvinethicalhacker at gmail com for the great the work you done for me, i got the email address on the net web when i needed to hack my husband cell phone he helped me within few hours with whatsApp hacking and GPS location tracking direct from my person phone i know how my husband walks, thanks for the helped you do for me for every grateful for your helped, you can contact him through gmail via kelvinethicalhacker at gmail.com or Telegram, calls, text, number +1(341)465-4599, if you are in needed of hacking services, contact him..
A great hacker is really worthy of good recommendation , Henry
really help to get all the evidence i needed against my husband and
and i was able to confront him with this details from this great hacker
to get an amazing service done with the help ,he is good with what he does and the charges are affordable, I think all I owe him is publicity for a great work done via, Henryclarkethicalhacker at gmail com, and you can text, call him on whatsapp him on +12014305865, or +17736092741,
Hi, colorsheme looks good, provide the color scheme name or links to GitHub?