No products in the cart.
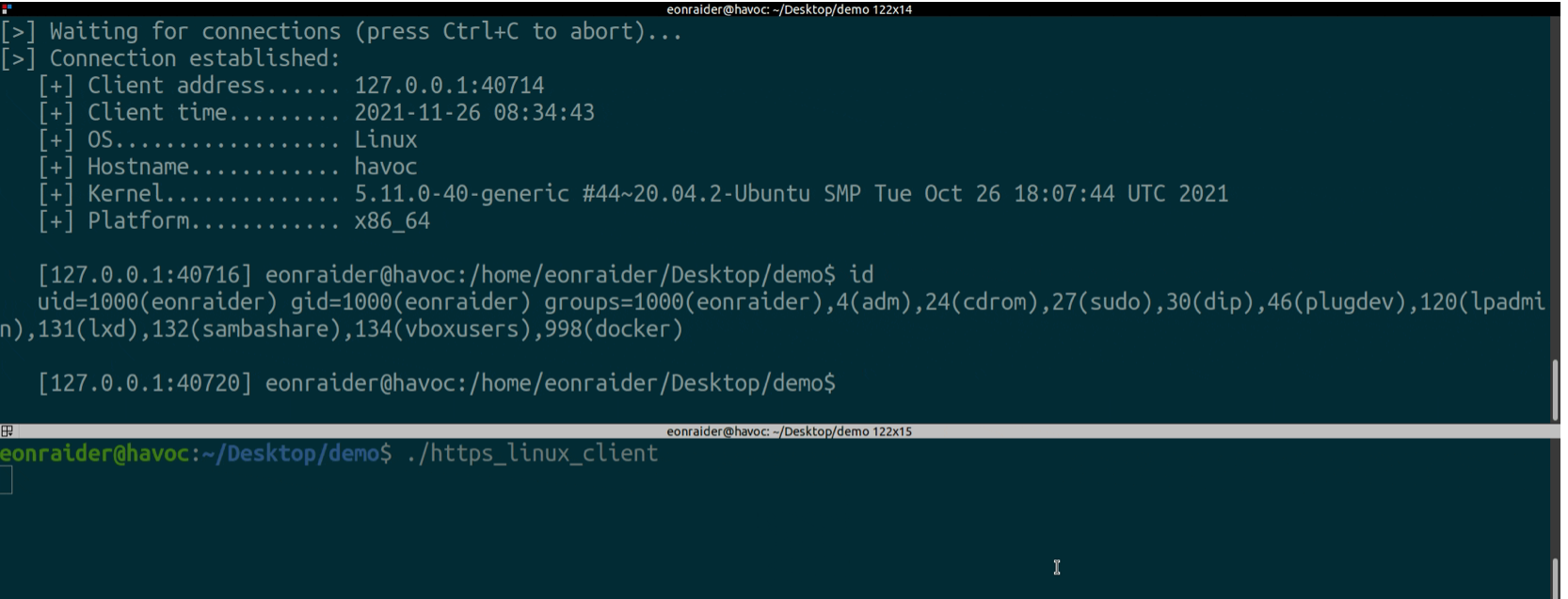
Phantom is a multi-platform HTTP(S) Reverse Shell server and client in Python 3. Binaries for Linux and Windows platforms can be built through an embedded script that executes PyInstaller. Reverse shells can be established through HTTP or HTTPS. The certificates used for HTTPS can be auto-generated by Phantom or supplied by the user. Phantom includes a helper shell script that enables the fast generation of self-signed certificates for use of both servers and clients. After generation, the server and certificate authority certificates required for encrypted connections are bundled in the binaries for portability and ease of execution. Demo Try it out! Simply head over to the dist directory and download the pre-built Linux/Unix or Windows binaries. The HTTP client files are set to connect to https://localhost:8080, whereas the HTTPS client bundles a CA certificate file for https://localhost:4443 and will only connect to this socket. With that in mind, choose either....
A very big thanks to kelvinethicalhacker at gmail com for the great the work you done for me, i got the email address on the net web when i needed to hack my husband cell phone he helped me within few hours with whatsApp hacking and GPS location tracking direct from my person phone i know how my husband walks, thanks for the helped you do for me for every grateful for your helped, you can contact him through gmail via kelvinethicalhacker at gmail.com or Telegram, calls, text, number +1(341)465-4599, if you are in needed of hacking services, contact him.
A great hacker is really worthy of good recommendation , Henry
really help to get all the evidence i needed against my husband and
and i was able to confront him with this details from this great hacker
to get an amazing service done with the help ,he is good with what he does and the charges are affordable, I think all I owe him is publicity for a great work done via, Henryclarkethicalhacker at gmail com, and you can text, call him on whatsapp him on +12014305865, or +17736092741,