No products in the cart.
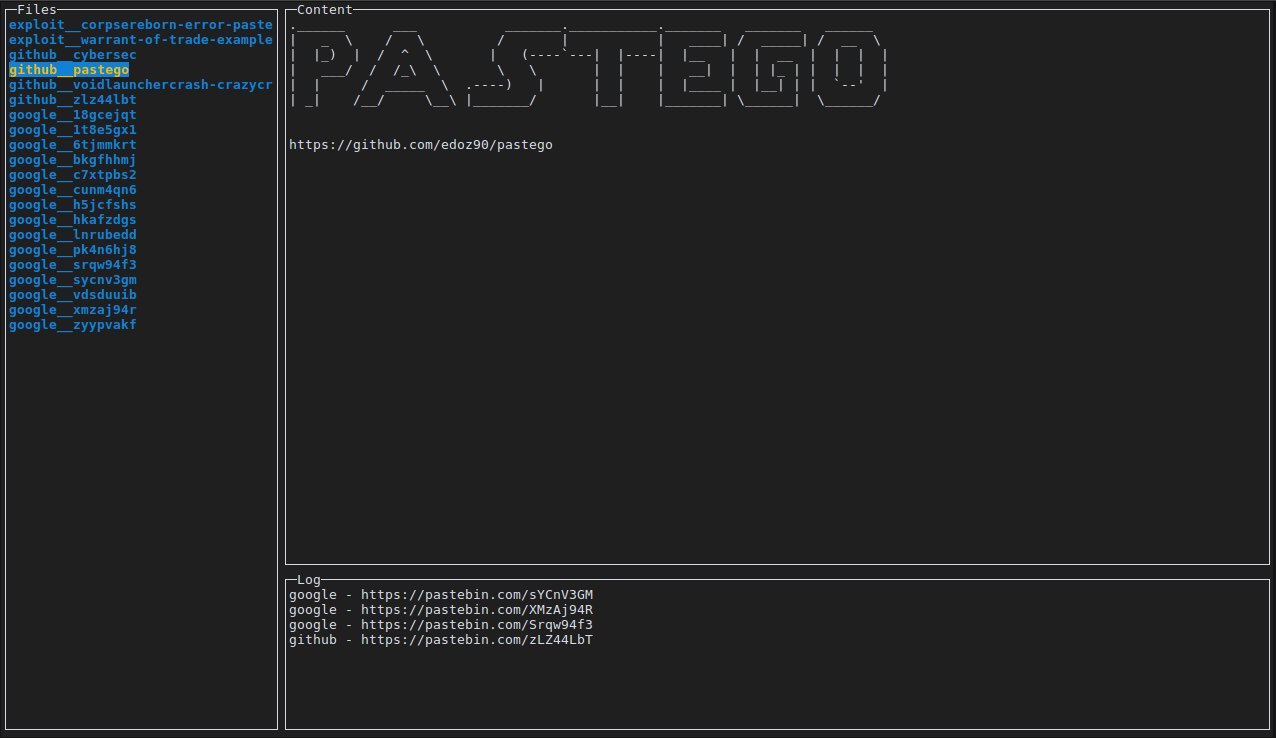
pastego is a scrape/Parse Pastebin using GO and grammar expression (PEG). Installation $ go get -u github.com/notdodo/pastego Usage Search keywords are case sensitive pastego -s "password,keygen,PASSWORD" You can use boolean operators to reduce false positive pastego -s "quake && ~earthquake, password && ~(php || sudo || Linux || '<body>')" This command will search for bins with quake but not earthquake words and for bins with password but not php, sudo, Linux, <body> words. usage: pastego [<flags>] Flags: --help Show context-sensitive help (also try --help-long and --help-man). -s, --search="pass" Strings to search, i.e: "password,ssh" -o, --output="results" Folder to save the bins -i, --insensitive Search for case-insensitive strings Supported expression/operators: `&&` - and `||` - or `~` - not `'string with space'` `(myexpression && 'with operators')` Keybindings q, ctrl+c: quit pastego k, ↑: show previous bin j, ↓: show next bin n: jump forward by 15 bins p: jump backward by 15....
Subscribe
0 Comments