No products in the cart.
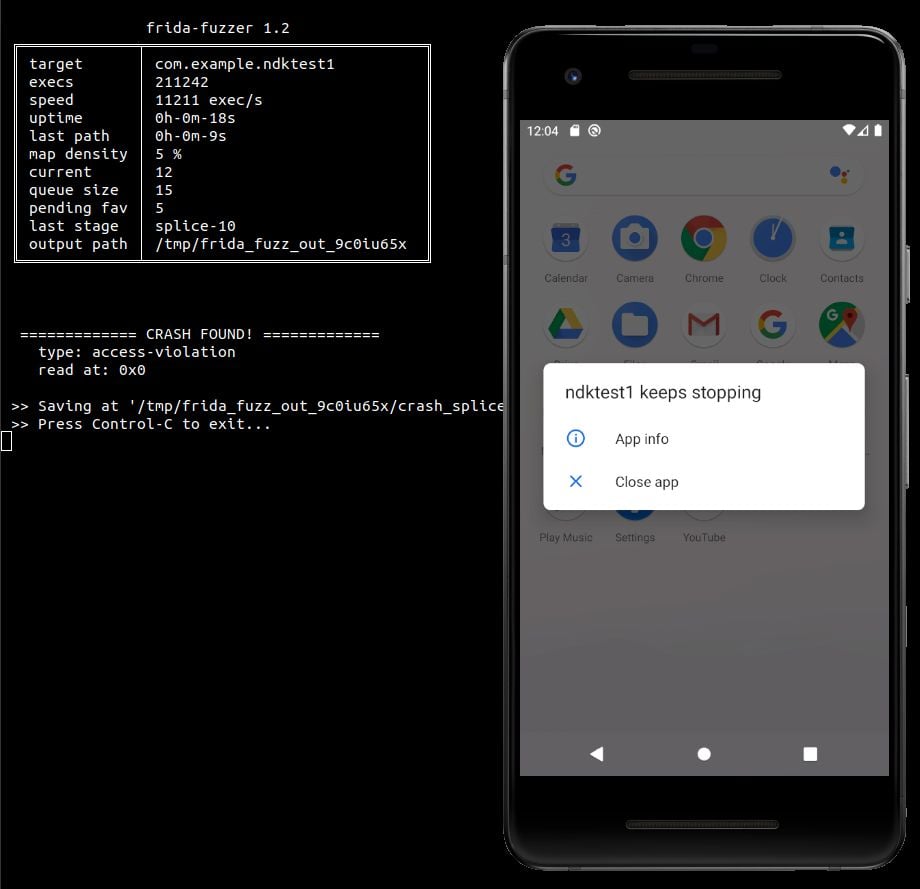
This experimental fuzzer is meant to be used for API in-memory fuzzing. The design is highly inspired and based on AFL/AFL++. ATM the mutator is quite simple, just the AFL's havoc and splice stages. I tested only the examples under tests/, this is a WIP project but is known to works at least on GNU/Linux x86_64 and Android x86_64. You need Frida >= 12.8.1 to run this (pip3 install -U frida) and frida-tools to compile the harness. Usage The fuzz library has to be imported into a custom harness and then compiled with frida-compile to generate the agent that frida-fuzzer will inject into the target app. The majority of the logic of the fuzzer is in the agent. A harness has the following format: var fuzz = require("./fuzz"); var TARGET_MODULE = "test_linux64"; var TARGET_FUNCTION = DebugSymbol.fromName("target_func").address;; var RET_TYPE = "void"; var ARGS_TYPES = ['pointer', 'int']; var func_handle = new NativeFunction(TARGET_FUNCTION, RET_TYPE,....
Subscribe
0 Comments