No products in the cart.
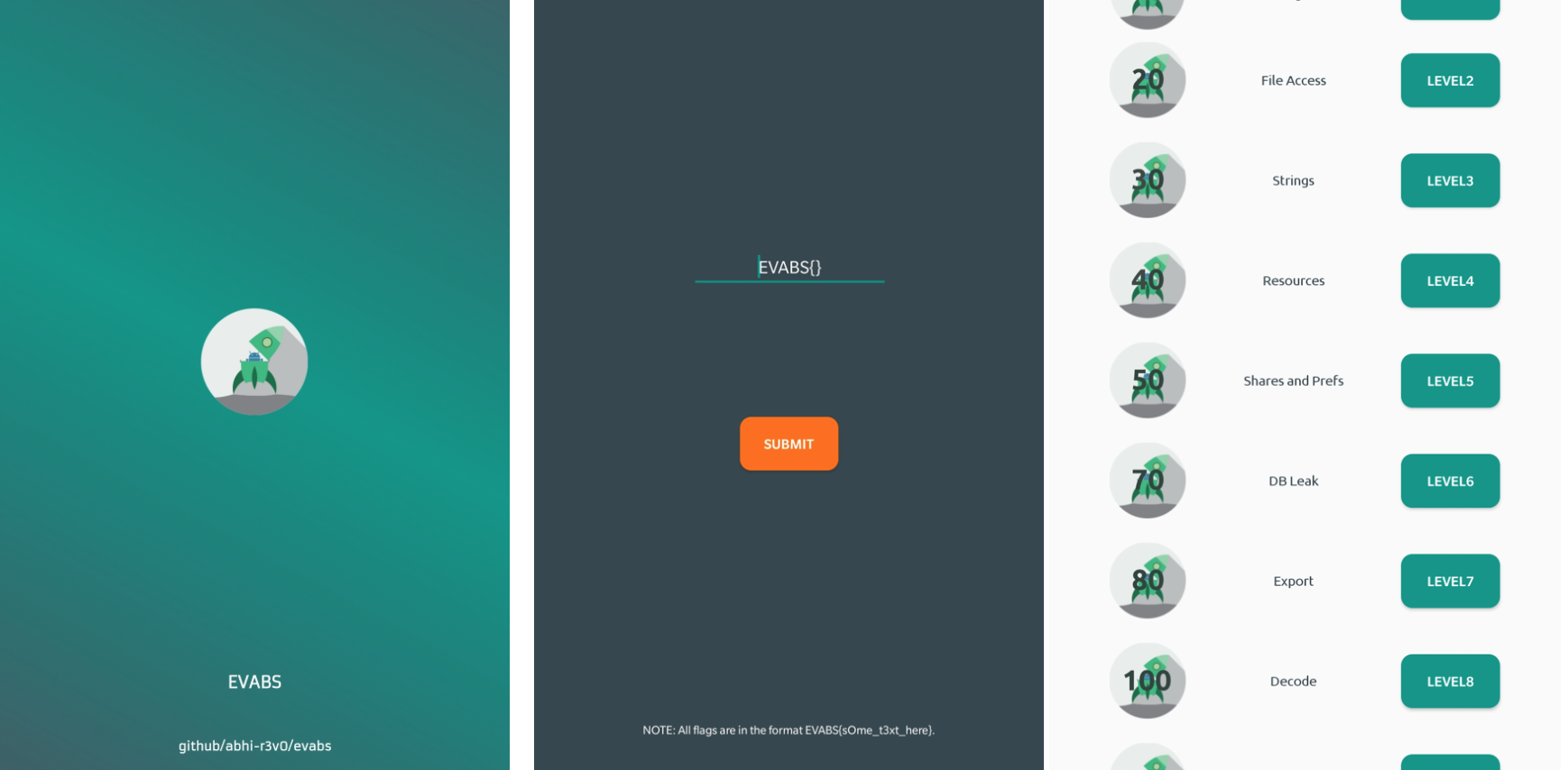
An open source Android application that is intentionally vulnerable so as to act as a learning platform for Android application security beginners. The effort is to introduce beginners with very limited or zero knowledge to some of the major and commonly found real-world based Android application vulnerabilities in a story-based, interactive model. EVABS follows a level-wise difficulty approach and in each level, the player learns a new concept. This project is still under progress and aims at incorporating as many levels as possible. For complete details and solutions, head to the blog series. INSTALLATION Download the latest application file from the releases page. Install it in an Android device (rooted recommended) or emulator. (Head to this blog for more information) SCREENSHOTS: REQUIREMENTS Android Emulator (Default/Genymotion) or a rooted Android device. FRIDA ADB apktool dex2jar or use ADHRIT (all-in-one tool) Confused? Read the documentation on setting up the environment. CHANGE....
Subscribe
0 Comments