No products in the cart.
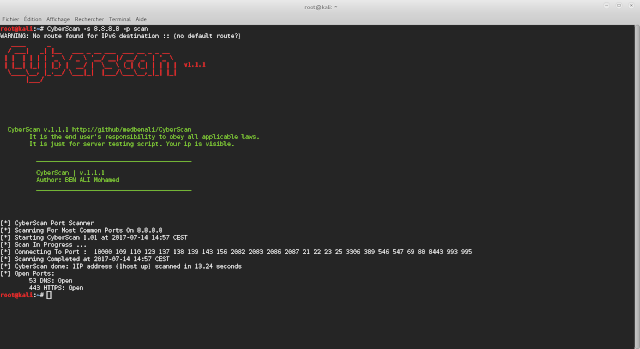
This article is from Hakin9 OPEN – Open Source Tools edition, which is available for download for free. Although it might seem that there are tons of similar tools, most of them serve a particular need, or offer complex technical features for a cybersecurity measurement requirement. In this article, we present Cyberscan, an easy to use tool that ensures together features of tools such as Nmap, Zenmap, Wireshark, etc. But, CyberScan is very simple and compact. It is an open source toolkit for pentesting and ethical hacking. For instance, CyberScan port scanner prevents intrusions by showing you the status of your network exposure by scanning the network to monitor open services and ports that can be exploited by exogenous traffic. Furthermore, it provides basic views of how the network is lead out in order to help identifying unauthorised hosts or applications and network host configuration errors that can cause serious security....
I was suspecting my husband was cheating on me and lying about it to my face. Thanks to my friend, she connected me to this great hacker. He spied on my husband’s phone, gave me access to everything on his phone, his email conversations, text messages and phone conversations and a whole lot more. This hacker is one of the best ever, his email address is [email protected] if anyone ever needs his service. He’s reliable and efficient and you can text,call or whatsapp him on +13134033941 .,.,.
intresting