No products in the cart.
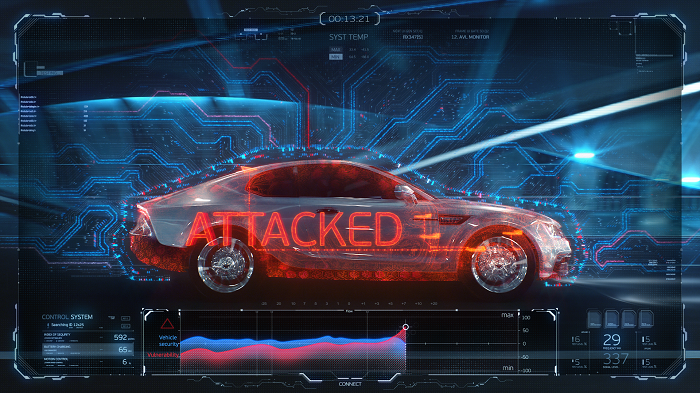
This is the second part of the series "Car Hacking: The Ultimate Guide!". In Part I, we discussed what a CAN Bus is, some information to get you started with CAN Traffic, and how to set up a virtual Car Hacking system using ICSim. In this place, we will dive deep by sniffing the car data through CAN Traffic. What does a CAN message look like? This is exactly what messages from CAN look like when they are recorded. If I break the columns, the first is the interface, the second is the arbitration ID, the third is the size of the CAN message, it can not be larger than 8 (If you look at the CAN framework, you will better understand why this can not is greater than 8), the fourth is the CAN data itself. The meaning of the CAN message In this example, we will see an....
I tried to access Part 1 thru this link
vhttps://hakin9.org/car-hacking-the-ultimate-guide-part-i/
But , Page not found error came.
Can you please give me link for Part 1
A very big thanks to kelvinethicalhacker at gmail com for the great the work you done for me, i got the email address on the net web when i needed to hack my husband cell phone he helped me within few hours with whatsApp hacking and GPS location tracking direct from my person phone i know how my husband walks, thanks for the helped you do for me for every grateful for your helped, you can contact him through gmail via kelvinethicalhacker at gmail.com or Telegram, calls, text, number +1(341)465-4599, if you are in needed of hacking services, contact him.
A great hacker is really worthy of good recommendation , Henry
really help to get all the evidence i needed against my husband and
and i was able to confront him with this details from this great hacker
to get an amazing service done with the help ,he is good with what he does and the charges are affordable, I think all I owe him is publicity for a great work done via, Henryclarkethicalhacker at gmail com, and you can text, call him on whatsapp him on +12014305865, or +17736092741,
Hello Anastasis,
I have followed your training and it is absolutely fascinating. Can we connect in Linkedin?
Would like to learn more about Car hacking and hardware involved for physical connected car