No products in the cart.
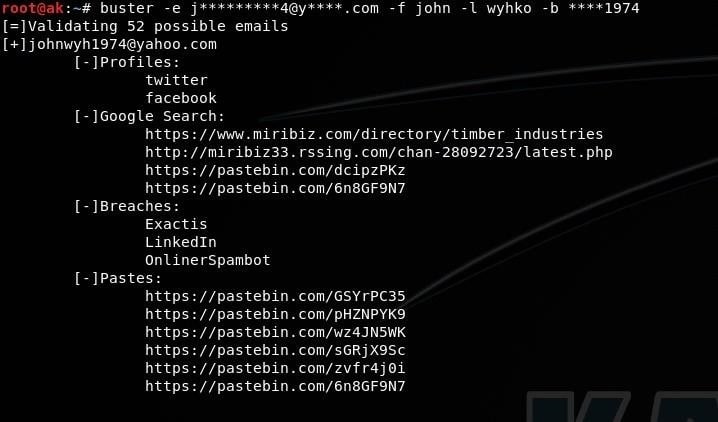
Buster is an advanced OSINT tool used to: Get social accounts of an email using multiple sources(gravatar,about.me,myspace,skype,github,linkedin,previous breaches) Get links to where the email was found using google,twitter,darksearch and paste sites Get breaches of an email Get domains registered with an email (reverse whois) Generate possible emails and usernames of a person Find the email of a social media account Find emails from a username Find the work email of a person Installation clone the repository: $ git clone git://github.com/sham00n/buster Once you have a copy of the source, you can install it with: $ cd buster/ $ python3 setup.py install $ buster -h API keys This project uses hunter.io to get information from company emails,the first couple "company email" searches dont require a key,if you have an interest in company emails i recommend that you sign up for an account on hunter.io. Once you get an API key, add it....
Subscribe
0 Comments